Master Key or Master Lie? How authority and confidence bypass securityWhen “I’m the boss” walks in, verification walks out.
- Captain Ajesh Sharma (Veteran)

- Feb 17
- 3 min read

Authors:
Katarzyna Kałużny, Global Leader in Operations & Enabling Functions, Executive MBA
Capt. Ajesh Sharma, Global Security Strategist & Leader, Founder of Helix Security Advisors
Master Key or Master Lie?
“Hi. I’m from HQ.”
“Internal audit.”
“IT support — outage. I need access now.”
Uniforms, badges, confident tone– the higher stress, the faster the obedience. Most physical security breaches don’t start with force. They start with authority convincingly performed.
Across industries and geographies, one pattern repeats with unsettling consistency: people obey tone of voice faster than they verify credentials. A confident command, delivered with the right posture, uniform, or badge, can override established controls faster than any technical vulnerability.
This phenomenon is known as authority bias — our tendency to comply with individuals who appear powerful, official, or legitimate, even when proof is missing.
The Authority Playbook: how proof gets overridden
Attackers don’t need sophistication. They need a stage — and a convincing performance.
Almost always, it’s built from the same three ingredients:

Costume Uniform, badge, lanyard, clipboard, branded hoodie.

Urgency
Urgency “I’m late.” “There’s an incident.” “This is time-critical.”

Consequences “Don’t you know who I am?”, “Who’s your manager?”, “I’ll make sure you’re sacked.”
None of this is proof. It’s pressure.
A classic example of authority bias in action is the Isabella Stewart Gardner Museum heist in Boston. In the early hours of the morning, two thieves gained access by impersonating police officers responding to a disturbance. Speaking confidently through the intercom and claiming lawful authority, they were admitted without proper verification. Once inside, they restrained the guards and stole 13 priceless works of art. The theft remains one of the most significant unsolved art crimes in history.
In corporate environments the outcome is usually smaller — but the mechanism is identical:
authoritative tone
executive name-dropping
urgency
verbal pressure at entry points
When identity verification is challenged, a response delivered in a deep, assertive, authoritative voice should not reassure — it should raise a red flag.
Why Verification Collapses Under Pressure
Authority bias works because our brains treat status cues (uniforms, titles, confident tone) as a fast shortcut for legitimacy — often before we’ve seen real proof. Classic obedience research shows how easily people defer to “legitimate authority,” especially in structured environments where responsibility feels shared or “above our pay grade.”
Social engineers then add two accelerators: urgency (which narrows attention and reduces scrutiny) and consequences (“Who’s your manager?”). That combination shifts people from “verify” to “comply” — not because they’re careless, but because the situation feels socially and professionally costly to challenge.
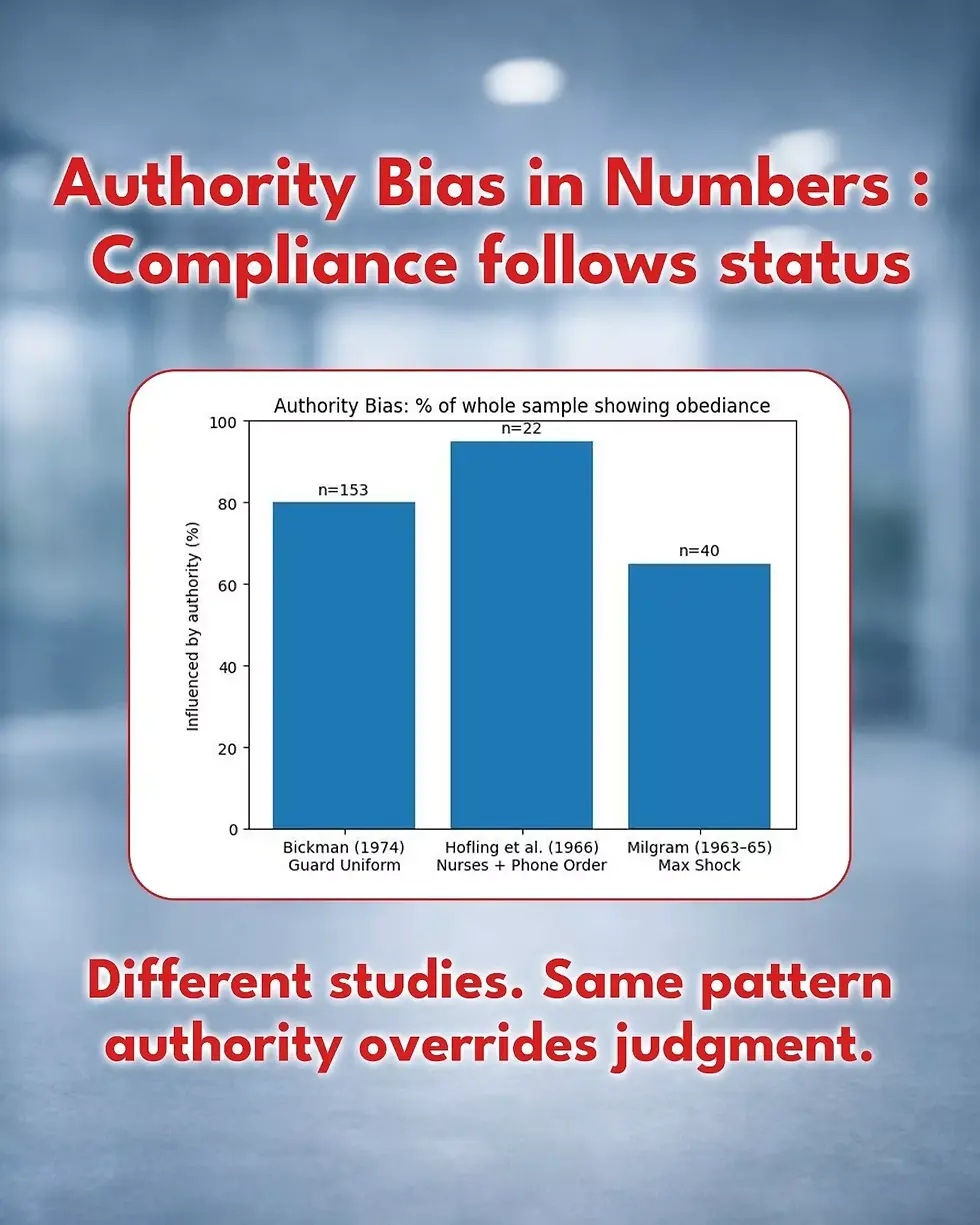
Authority bias isn’t subtle — it’s measurable and repeatedly observed. Research shows that a uniform can pull ~80% compliance. A confident “doctor” on the phone pushed 21/22 nurses (≈95%) toward an unsafe action. And in classic Milgram obedience test, 65% went all the way when authority felt legitimate. In other words: a confident badge doesn’t just open doors — it exploits predictable human decision shortcuts under pressure.
The Core Security Lesson
Verification fails precisely when hierarchy enters the room.
Authority — real or perceived — has a way of silencing process. This is where breaches are born. Trust your intuition. If something feels wrong, it usually is.
Genuine, legitimate individuals typically:
Answer verification questions clearly and directly
Provide credentials without resistance
Move on quickly to their actual task
Those with something to hide often do the opposite. They challenge the question itself, attempt to intimidate the verifier, or escalate emotionally. Authority is performed, not demonstrated.
What Needs to Change
Security is not a frontline task — it is a leadership responsibility. When people fear consequences for pausing access or questioning a confident badge, controls don’t weaken — they collapse.
Leaders must visibly support personnel who pause access to verify credentials.
At the same time, entry processes must be simple, explicit, and non-negotiable.
Complexity creates hesitation, and hesitation is exactly what authority exploits.
Clarity builds confidence. Confidence sustains compliance.
And here’s the uncomfortable truth: “Security that doesn’t annoy anyone usually doesn’t work.”
Effective security creates friction — especially for those relying on a confident badge instead of legitimate proof. A raised voice, a commanding tone, or verbal dominance must never intimidate the person doing their job. Verification is not an insult — it is a process.
If “I’m from HQ” walked in today and turned up the pressure — would your team verify… or comply?

#SocialEngineering #SecurityAwareness #HumanFactors #OperationalRisk #SecurityLeadership #TrustButVerify
Authors:
Katarzyna Kałużny, Global Leader in Operations & Enabling Functions, Executive MBA
Capt. Ajesh Sharma, Global Security Strategist & Leader, Founder of Helix Security Advisors
.png)



Comments